Analyze this tweet and see if you can crack the code. Tore Says is a known cryptographer, which involves hiding secret messages. Take your best shot:

Did you solve the riddle?
OY VEY, sans the “Y” is OVE. Swap the letters around and we get: Operation Ernest Voice. That’s solid steganography that most missed. Now, what exactly is Tore Says asking Elon to disclose about his recently acquired company, Twitter? She has warned us that Twitter has longstanding MOUs, Memorandums of Understanding, with nations. And that includes the country of Twitters origin, the Untied States.
Tore, an intelligence contractor, has disclosed in the documentary, ShadowGate, that she coordinated, hence her Twitter handle as Chaos Coordinator, internet influence activities in the Middle East. PsyOps are psychological operations also known as PsyWar.
PSYWAR
Psychological Operations is a well known and publicly verifiable department, yet many citizens don’t know about it. Let’s allow the public record of the US Army to explain what it is and who they are. On May 2, 2022, The US Army 4th PsyOp Division released a YouTube video titled Ghosts in the Machine which has stirred much interest with over 1 million views. If you create a list of the historical events in this video you will notice the following:
World War 2 inflatable tank props to fool the Germans on troop movements
Vietnam War pamphlets released from a plane
Cold War conflict with Russia
1989 Tiananmen Square protests and massacre in China
Iraq War in which Saddam Hussein was deposed while a TV camera captured a toppling statue
2014 Ukraine protest riots and other Arab Spring riots in the Middle East
All of this is a pretty stunning admission to the public regarding their activities; especially the riots. So many people have been used like puppets to completely overthrow governments. A specific example is well documented in Ukraine’s 2013-2014 Maidan Uprising with the US Assistant Secretary of State Victoria Nuland becoming internet famous for her leaked conversation with the US ambassador to Ukraine. This audio clip is purportedly between Nuland and the US Ambassador to Ukraine, Geoffrey Pyatt. They are heard discussing strategies to deal with opposition figures. It is just one example of manipulating the opposition; in this case, Ukrainian.
You must draw from your own studies of history and come to your own conclusions on what the PsyOp division of the US military honestly did. It is irrefutable that they are confirming and promoting their involvement while inviting others to join, as this is a recruitment effort. In the end, they are unseen ghosts in the machine of our world, seeking to deceive and influence, with results under the cover of secrecy. They disclosed their involvement in historical events in the video, or perhaps deceived you about their involvement in some.
Consider another PsyOp example such as the declassified release of the CIA operation depicted in the movie ARGO; deceiving a nation with a fake movie all to achieve a military objective. That is PsyWar; deception and influence on an intended target to push them toward or contain them within the thinking of the PsyOp goals.
OEV Origins
Operation Earnest Voice (OEV) was first developed in Iraq as a psychological warfare weapon against the online presence of al-Qaeda supporters and others ranged against coalition forces. Since then, OEV is reported to have expanded into a $200 million program and is thought to have been used against jihadists across Pakistan, Afghanistan, and the Middle East. In a 2011 Washington Post article we learn:
General David H. Petraeus, the US Central Command Commander, said that CENTCOM’s communications program, Operation Earnest Voice, will “reach regional audiences through traditional media, as well as via web sites and regional public-affairs blogging.”
General James Mattis, the successor of Gen. Petraeus told Congress “In each of these efforts, we follow the admonition we practiced in Iraq, that of being first with the truth,” he added.
Mattis said that Taliban propagandists are using the internet for recruiting.
“We can directly track some of this. In broad terms, we challenge their propaganda. We disrupt the recruiting. We show that it’s silly to go down this line. . . . We bring out the moderate voices. We amplify those. And in more detail, we detect and we flag if there is adversary, hostile, corrosive content in some open-source web forum, [and] we engage with the web administrators to show that this violates web site provider policies.”
General James Mattis, told the same committee that OEV "supports all activities associated with degrading the enemy narrative, including web engagement and web-based product distribution capabilities.”
A 2011 Guardian article by Nick Fielding and Ian Cobain was the first one to break the story and served as an early wake up call to the US taxpayers. They discovered that the US military was developing software that allowed it to secretly manipulate social media sites by using fake online personas in order to influence internet conversations and spread pro-American propaganda. The software allowed one person to control up to ten separate identities all over the world. Each fake online persona required a convincing background, history, and supporting details. The project was viewed as similar to China's attempts to control and restrict free speech on the internet. The software allowed US service personnel to respond to emerging online conversations with coordinated messages, blog posts, chatroom posts, and other interventions. The project was developed under OEV. OEV was managed by the multinational forces and was developed to communicate critical messages and to counter the propaganda of adversaries. The article discusses the legal challenges the project would face if turned against US citizens, where people engaged in sock puppetry have faced prosecution.
A California corporation has been awarded a contract with United States Central Command (USCENTCOM), which oversees US armed operations in the Middle East and Central Asia, to develop what is described as an "online persona management service" that allows one US serviceman or woman to control up to ten separate identities based all over the world. CENTCOM confirmed that the $2.76 million contract was awarded to Ntrepid, a newly formed corporation registered in Los Angeles. It would not disclose whether the multiple persona project is already in operation or discuss any related contracts.
United States Central Command
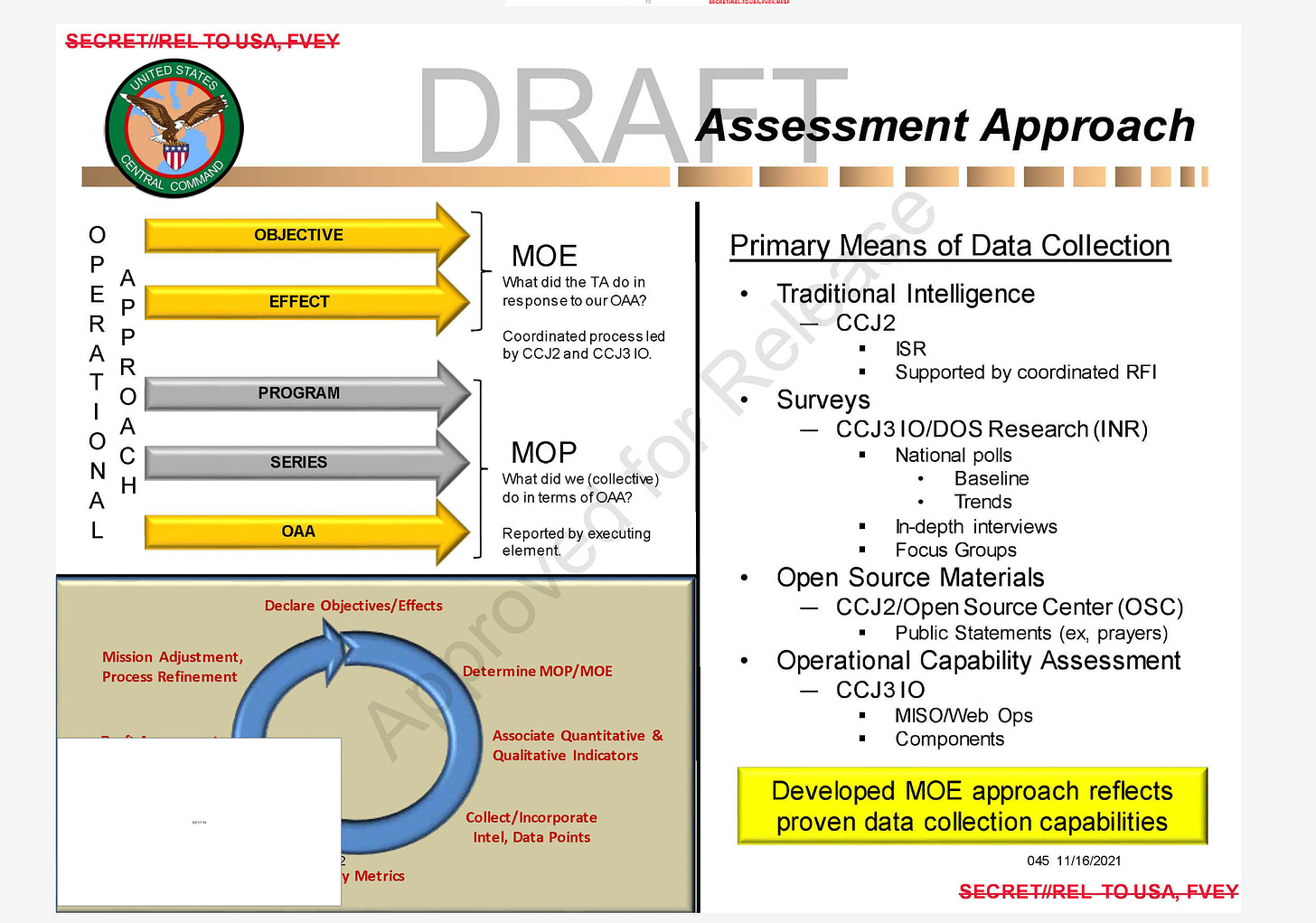
In January of 2023, after many denials and delays, The Black Vault was finally able to obtain a 145 page PDF on Operation Earnest Voice; in addition to the fourteen pages they received in 2022. These declassified documents of the 2022 release uncovered by The Black Vault which are excerpts from pages 4-13, outline the following factors:
MISSION. USCENTCOM, in Coordination and Collaboration With DOS (Department of State), Other USG (U.S. Government) Agencies, and Partner
MISSION. USCENTCOM, in coordination and collaboration with DOS (Department of state), other USG (U.S. Government) Agencies, and partner nations, truthfully informs, persuades, and influences audiences in support of the commander’s theater strategy and campaign plans.
3.A.4. Concept of operation… achievement of theater objectives. Operations, actions and activities will focus on countering enemy propaganda with regional implications, amplifying moderate voices within the region, and driving an ideological wedge to disrupt the enemy narrative.
3.B.1.B. Plan and conduct psyop and civil military operations in targeted nations within the area of responsibility, in support of oev objectives.
3.B.1.D. Develop Long term plan to counter extremist ideology and propaganda.
3. B .1. E. Plan and conduct psyop iso unconventional warfare.
3.C.4. Department of state.
4.0.1. USCENTCOM has received approval at the office of the secretary of defense for funding to support OEV through its Executive Agent for fiscal year 2009 and has been established as a program of record for fiscal year 2010-2015. Authorized funding for fiscal year 2010 is $75 million.
It’s important to note that operations were funded from 2009-2015. On page 22 of the 145 page OEV declassified documentation, the tables show that OEV and its predecessors received funding back in 2005.
February (2011), the multimedia publication Information Week was among the first to publish a story about CENTCOM’s 2010 contract with a California company. The solicitation called for supplying software to allow a military operator in Afghanistan to create and control 10 Web personalities “replete with background, history, supporting details and cyber presences that are technically, culturally and geographically consistent.” These virtual persons are to be untraceable and “must be able to appear to originate in nearly any part of the world and can interact through conventional online services and social media platforms,” according to the contract proposal.
Now look at a diagram from the January 2023 released documents to understand who the target nations are:
Nations with existing ISIL troops receive a Priority 1 rating which includes: Iraq, Syria, Afghanistan, Pakistan, Egypt, Yemen and Saudi Arabia. Nations with potential ISIL connections are considered to be Priority 2: Lebanon, Kuwait, Jordan, Qatar, Bahrain and the United Arab Emirates. Existing ISIL sentiment of support nations received Priority 3 focus: Uzbekistan, Oman, Kyrgyzstan, Tajikistan, Turkmenistan, Kazakhstan and Iran. This is a wide target range.
On page 46 from the January 2023 declassified OEV document, we can also see that methods of data collection include traditional intelligence surveys (does anyone trust those these days?), open source materials and Military Information Support Operations (MISO) web ops.
PsyWar in the Desert Storm
The Iraq invasion of Kuwait happened due to an OPEC oil pumping limit violation as Kuwait held debt from the Iraq-Iran war from 1980 through 1988. So Operation Desert Storm commenced to remove Iraq from the very small nation of Kuwait. In charge of the military operation was General Norman Schwarzkopf who had a team of “Jedi Knights” that developed the battle plan. And our investigations reveal that tactics included Voice of God' technologies which compelled the enemy combatants to lay down their weapons without fighting. As the General said, they developed a “winning strategy.”
During the Gulf War requested PSYOP were denied by various agencies and staffing bureaucracy within DOD due to sensitivities to coalition partners. Schwarzkopf’s patience was wearing thin as he stated, “Psychological Operations are going to be absolutely critical, critical part of any campaign that we must get involved in.” As a result of the media campaigns, news agency operations and other unknown PsyWar tactics, a sweeping victory was achieved with minimal casualties. And the U.S. Department of Defense hailed this as “one of the most successful ground operations in the history of war.”
Data Leak Revelations
Operations have been a part of the Department of Defense’s War on Terror since September 20, 2001’s declaration of war by George W. Bush in the US Congress. These operations use the tools of PsyWar and information in order to avoid lethal conflict. In 2017, a Cyber Risk Team discovered US CENTCOM and PACOM (Pacific Command) data on a public Amazon web server started by a 3rd party contracted company named VendorX. This revealed new information on data collection and operations primarily in Afghanistan and Pakistan. The data captured included news sites, comment sections, web forums, and social media sites like Facebook; featuring multiple languages and originating from countries around the world. Among the data stolen from Americans, much seems benign: social media posts, and public internet addresses. This points to an apparent Pentagon intelligence gathering operation that raises serious questions about privacy and civil liberties.
In a 2017 pentagon public hearing, Major Josh Jacques, a spokesman for US CENTCOM made these public comments in response to backlash from the data breach:
"The information you are asking about is not sensitive information. It is not collected nor processed for any intelligence purposes."
"US Central Command has used commercial off-the-shelf and web-based programs to support public information gathering, measurement and engagement activities of our online programs on public sites."
"The information is widely available to anyone who conducts similar online activities."
Several folders were discovered containing this data ranging from 2009 to 2017, when the discovery was made. The folders were labeled CENTCOM, OUTPOST, INGEST and CORAL; the last folder a reference to US Army software. Their website says:
An application called Coral Reef which is part of the Army's larger Distributed Common Ground System was named one of the Top 5 among 25 top technologies and efforts of 2012.
The Coral Reef software allows users of intelligence to better understand relationships between persons of interest. The software users first gain access to the portable electronics devices of targets such as GPS receivers and cell phones. The information is then uploaded to the Coral Reef software.
In summary, the US military is focused on proactive postings within other countries as well as data from US citizens.
In a November 17, 2017 CNN article, another expert, Andrea Little Limbago, Chief Social Scientist at cybersecurity firm Endgame, said that it's not uncommon for the Pentagon to collect vast sums of internet data.
"At times, you do need to cast a wide net, and then do the analytics to narrow down what you're trying to find," said Limbago, a former analyst with the Defense Department between 2007 and 2011.
She said that she would be surprised if the Defense Department was targeting U.S. individuals without the proper authorization.
This is concerning since in 2011 US Central Command went on record advocating for non-domestic activity.
A spokesman for the US Central Command region, which includes the Middle East, Pakistan and Afghanistan, said that the psychological warfare scheme was operating only on overseas social media sites.
"We do not target US audiences, and we do not conduct these activities on sites owned by U.S. companies," he said.
source: 2011 Telegraph article
Operation Gridlock, Smith-Mundt Act & Foreign Relations Authorization Act
In her November 26, 2018 article, Tore Says discusses the Smith-Mundt Modernization Act which was introduced by Republican politician Mac Thornberry. This act legalized domestic distribution of information and material about the United States that was primarily intended for foreign audiences, to now be viable for use on US citizens. That is foreign war propaganda, now legally deployed domestically, on you.
Buzzfeed reported that the act would neutralize two previous acts: 1. the Smith-Mundt Act of 1948 and 2. the Foreign Relations Authorization Act in 1987, that had been passed to protect US audiences from government misinformation campaigns. The article also highlights the Obama administration's use of social media in campaigns and how the Pentagon used specialized software to monitor and influence Twitter debates. The article concludes by stating that the Pentagon has been building up the foundations to privatize the infinite web so that the unlimited access to information can be controlled, potentially turning tyrannous and reaching all aspects of communication and information access for the interests of the 1%.
Tore Says wrote an article on March 20, 2022 describing many key truths about the Truth Social media platform. Despite Truth Social’s claims of free speech and truth, it is no different than many other platforms like Getter, Parler, or other conservative apps. They are echo chambers and data mining platforms. Operation Gridlock was an operation the United States conducted on foreign cybernetworks which weaponized the innate human need for “approval” of the masses and the superficial need for validation. Real truth and real news was choked and suffocated out by propaganda, re-tweets, followers, influencers, and propaganda trains. She points to the times of the 2020 election on twitter and beyond as a time of significant PsyWar and influence operations being conducted worthy of the title, Operation Gridlock.
We can’t say directly that the US military conducted operations on US soil, but it’s clear that the tactics developed and used in the Middle East were brought home to be used on the US population. Are we to conclude that private corporations are behind these operations? For political benefit? Perhaps contracted entities utilized for war operations returned home and built similar products and sold them to the highest bidder.
During a war, the tactics change, evolve, and advance. We have been in a very long-standing war, a world war, a digital war for control of all of humankind’s minds. If you fail to realize it, your message and products will become casualties.
Pentagon Information Pipeline
In a CNN article from November 13, 2019, we learn that in 2018 Facebook removed 3.3 billion fake sock puppet accounts and another 5.4 billion in 2019. In 2021 Facebook banned seven “surveillance-for-hire” companies from its platforms, including: Black Cube (Israel), Cobwebs (Israel) and Cytrox (North Macedonia).
More significant is the takedowns in recent years by Twitter and Facebook of more than 150 bogus personas and media sites created in the United States which was disclosed last month by internet researchers Graphika and the Stanford Internet Observatory. While the researchers did not attribute the sham accounts to the U.S. military, two officials familiar with the matter said that U.S. Central Command is among those whose activities are facing scrutiny. Like others interviewed for this report, they spoke on the condition of anonymity to discuss sensitive military operations.
source: 2022 Washington Post article
Back in 2019 Tore Says was warning us of severe government actions with social media:
…in 2011, the Pentagon literally created algorithms and specific software to monitor and influence Twitter. So keep in mind, this is not going to happen without Twitter knowing.
…this military project executed through the Pentagon was to monitor the Twitter debates going on about Chelsea Manning's then known as Bradley Manning's pretrial hearings.
…they were seeing how we debate, how it amplifies and then what they did was they created bots and what were called then sock puppets, to drive conversations and measure that influence. Now, I don't think people understand just how important this piece of information is…
…did you know that DARPA had also funded a program to monitor, record and analyze actions and reactions of Twitter users? Facebook did this experiment that was reported … 2014
…The Guardian reported about it, how Facebook literally created an experiment to see how they can manipulate people's emotions by their news feed.
Source: Tore Says Show on November 26, 2019
On April 19, 2023 Tore shares how Elon is warning us about the concern of AI.
Twitter Files & AI
2023 revelations about Twitter actions, before the purchase by Elon Musk, in the time prior to and after the 2020 election show us a massive peak behind the curtains of power. Most egregious being the removal of a sitting United States President from their platform, just as Facebook did too. Clearly communicating that they consider themselves to be superior to governments of the world. Did the world hear that? At the time Twitter was using “automated” actions and “bots” to remove and flag information, in other words AI (artificial Intelligence). But an argument can be made the PsyWar programming of the human operators was just as morally faulty as the bots. How again are they different?
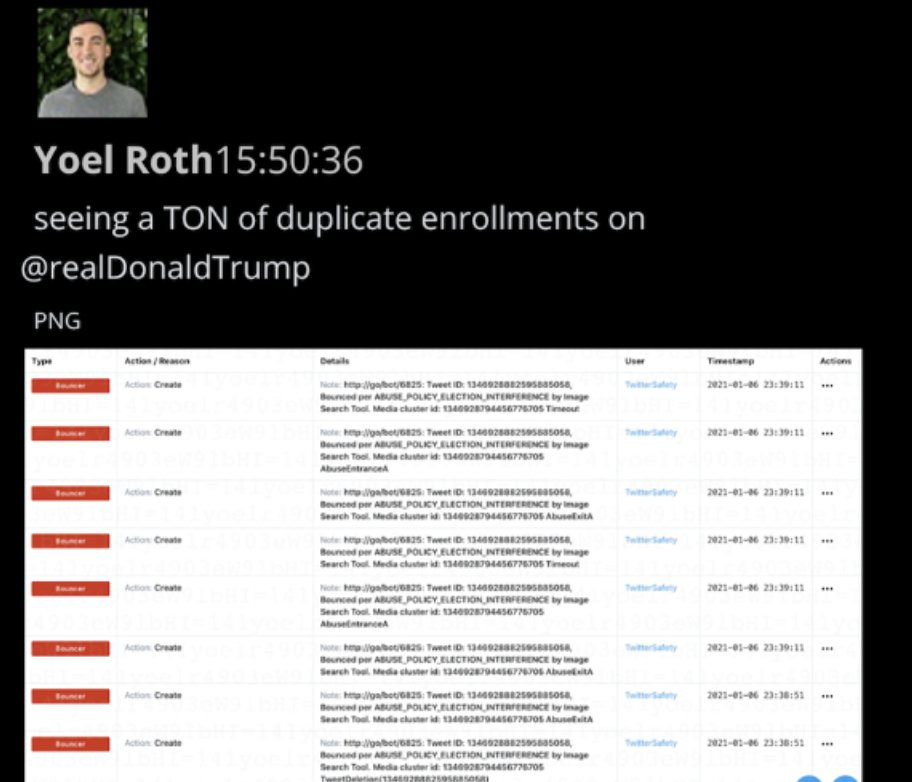
We learn of these AI bots in “The Removal of Donald Trump” article by Matt Taibbi in his Twitter files series, he states:
9. Before J6, Twitter was a unique mix of automated, rules-based enforcement, and more subjective moderation by senior executives. As reported, the firm had a vast array of tools for manipulating visibility, most all of which were thrown at Trump (and others) pre-J6.
49. In Twitter docs execs frequently refer to “bots,” e.g. “let’s put a bot on that.” A bot is just any automated heuristic moderation rule. It can be anything: every time a person in Brazil uses “green” and “blob” in the same sentence, action might be taken.
50. In this instance, it appears moderators added a bot for a Trump claim made on Breitbart. The bot ends up becoming an automated tool invisibly watching both Trump and, apparently, Breitbart (“will add media ID to bot”). Trump by J6 was quickly covered in bots.
63. A few last notes about January 6th. Roth at one point looked and found Trump had a slew of duplicate bot applications:
The Twitter Files also revealed corporate collusion with US government officials. In other words fascism. Which reveals the possibility of collaboration when there is supposed to be a separation of public and private interests. While most corporations protect their customer’s interests, twitter opened the front door. What was shown was a disturbing influence the FBI, DHS and CISA had over Twitter employees. Under the guise of foreign acts of war (through information), government federal employees labeled US citizens as disinformation agents and potentially linked to foreign entities. Emails were revealed from federal employees that they, without proof, merely because the citizens' opinion conflicted with that of the government employee’s preferred narrative.
How similar does the work of Operation Earnest Voice look compared to the Twitter Files?
Tore Says connects some incredible dots on a recent guest appearance on the Alpha Warrior Show:
The (competition) car is not gonna do what a Tesla does, because of the AI it has. [Elon Musk] can identify chat bots. In fact, the person that was warning Twitter safety, her name is Dell Harvey. But actually, that's not her real name. She was hired to allegedly monitor chat bots. But no one's interviewed her. Why? Cuz she's DARPA. And that's a fact. I've always made the argument. I even wrote articles that big tech is not private. It's like say your income is $100. If you're making $90, from the US government, does that make you a government contractor? Twitter has more than 90% Come in income coming in from governments? Well, they did with memorandums of understanding and agreements, and they're still in place. And how do I know that? I still haven't gotten my Twitter account back, because those are actually being used and sealed indictments against others. So there's a few people like the whistleblower for Uranium One, he hasn't gotten his Twitter account back. So those people that have not gotten their Twitter accounts back, are actually participating in active criminal investigations.
-Tore Says March 7, 2023
Looking Back to Look Forward
We are unwilling participants in this PsyWar that uses strategic OEV tactics not only overseas but also on US citizens. As discussed earlier, USCENTCOM is among many who are facing scrutiny. This level of intelligence gathering operations, data mining, surveillance companies for hire, and social relationship assets raises critical questions about privacy and civil liberties. Free speech, Constitutional rights and truth based news are what matter.
Did US citizens want former Twitter Executives Vijaya Gadde or Yoel Roth to be their EARNEST voice? Do they want the FBI, DHS and CISA or political parties to be their EARNEST voice? Or do people want the arguments in public for people to choose themselves?
The US government labeled PsyWar influence operations as “earnest.” With an intent for people to take and accept these messages as reality. What is the long term cost of manipulating and suppressing a human's ability to think independently? And the cost severed trust in institutions they once held in esteem? This compels the necessity of citizens to acquire knowledge themselves. To find the source information, and no longer rely on “authority” figures to tell us what to think. No one can know for you. You now must know yourself. You exist in a world of PsyWar that attempts to hijack and hack your reality. From many parties and interests. To overcome these you have to question everything. You are in charge as the authority of your own opinion.